In our digital world, managing data has become a crucial task, much like organizing a vast, complex library. This digital library is filled with all sorts of information – from important documents to personal records.
However, managing this data isn’t just about keeping it organized; it’s also about keeping it safe. This is where the challenges of data management in the digital age come into play.
Security is a key part of managing data. Imagine if someone could easily access or alter the information in our digital library. That would be risky, right? To prevent this, we use special security methods: encryption and authentication.
Encryption is like a secret code that scrambles our data so only people with the right key can read it. Authentication is like a security checkpoint that makes sure only authorized people can access the data. In this article, we’ll explore what role encryption and authentication play in securing data management.
Understanding Encryption in Data Management
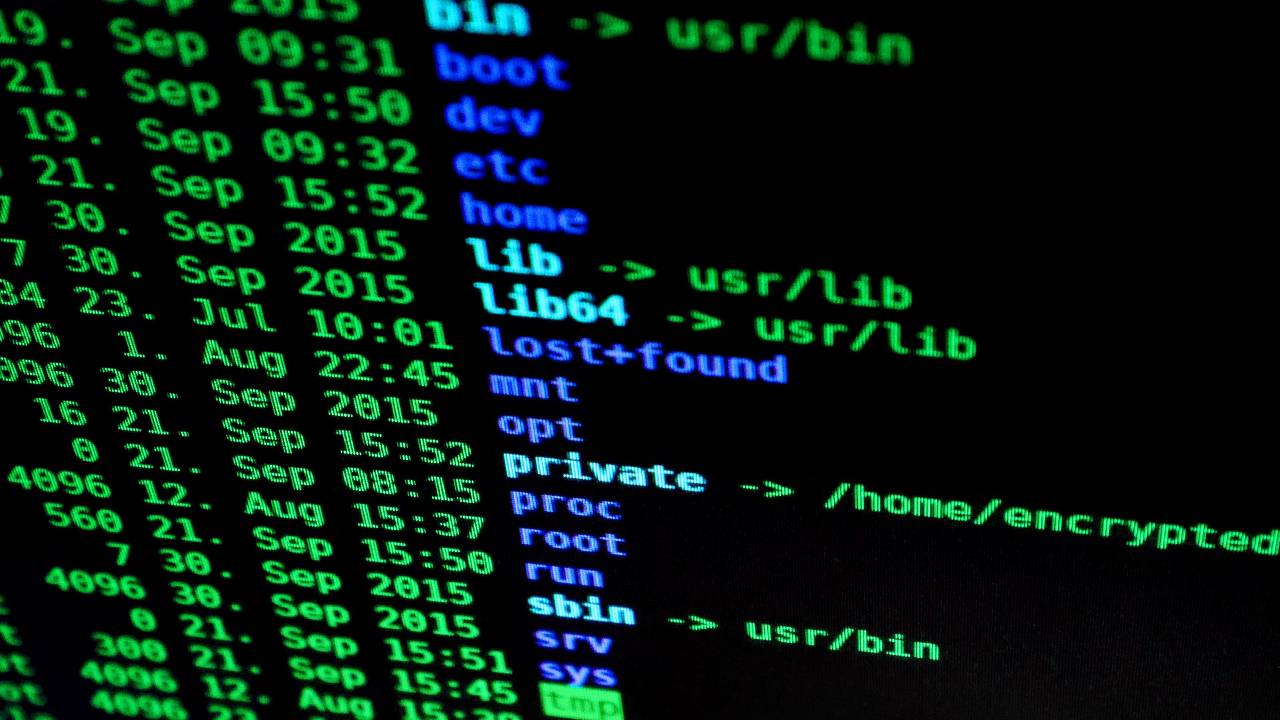
Encryption is a critical tool in the world of data management, acting as a digital guardian for our information. At its core, encryption is the process of converting data into a code to prevent unauthorized access.
Think of it as translating a message into a secret language that only those with the key, or decryption code, can understand. This process ensures that even if someone gets their hands on the data, they can’t read or use it without the correct key.
In an age where data breaches and cyber threats are increasingly common, encryption acts as a vital shield, keeping sensitive information like personal details, financial records, and confidential business data secure. Whether it’s a customer’s personal information or a company’s trade secrets, encryption helps in safeguarding this data from prying eyes.
In the realm of data management, various types of encryption are used to protect data, each with its own level of security and application. One of the most robust and widely used encryption standards is AES-256. AES stands for Advanced Encryption Standard, and the ‘256’ refers to the key size – 256 bits, which is known for its high level of security. This form of encryption is so strong that it’s used by governments and security agencies around the world to protect top-secret information.
AES-256 works by using a key, which is like a complex password, to scramble data. The data is transformed into a seemingly random series of characters that can only be turned back into its original form with the exact key used to encrypt it.
This level of encryption is particularly important in data management systems like ShareArchiver, where safeguarding data against unauthorized access is paramount. By employing AES-256, ShareArchiver ensures that the data it manages is not just stored and organized efficiently, but is also protected with one of the strongest encryption methods available today.
The Role of Authentication in Data Security
Authentication is a crucial component serving as the gatekeeper that controls access to information. It’s a process used to verify the identity of a user or a system before granting access to data. Think of it as a checkpoint that ensures only the right people can enter and view the digital information stored in systems.
Authentication helps prevent unauthorized users from accessing sensitive information, thereby protecting the data from misuse or theft. This is especially important in environments where multiple users have access to a shared system or network.
There are several methods of authentication, each adding a layer of security:
- Password-Based Authentication: This is the most common form. Users must enter a correct username and password to access the system. While effective, this method can be vulnerable if passwords are weak or shared.
- Multi-Factor Authentication (MFA): MFA requires users to provide two or more verification factors to gain access to a resource. This could be a combination of something they know (like a password), something they have (like a smartphone or a security token), and something they are (like a fingerprint or facial recognition). MFA significantly enhances security by adding multiple layers of defense.
- Biometric Authentication: This method uses unique biological traits of a person for verification, such as fingerprints, facial recognition, or iris scans. Biometric authentication is becoming increasingly popular due to its high level of security and ease of use. It’s difficult to replicate someone’s biometric data, making it a strong tool against unauthorized access.
- Token-Based Authentication: In this method, users are provided with a secure token, such as a key fob or a mobile app that generates a code. The user enters this code to access the system. Since the token is physically in the user’s possession, it provides an additional layer of security.
Integrating Encryption and Authentication
The integration of encryption and authentication in data management systems creates a formidable defense mechanism for enhancing data security. While each plays a vital role individually, their combined use provides a more comprehensive and robust security solution. This synergy is crucial in protecting sensitive data from various cyber threats and unauthorized access.
Layered Defense Strategy:
Encryption and authentication work together to create a layered defense strategy. Encryption acts as the first line of defense by encoding the data, making it unreadable to unauthorized users. Authentication adds another layer by controlling who can access the encrypted data. This dual-layer approach significantly reduces the risk of data breaches and unauthorized access.
Securing Data at Rest and in Transit:
Encryption ensures that data is secure both at rest (when stored) and in transit (when being transferred). Authentication enhances this by ensuring that only authorized users can access the data when it’s at rest and can initiate or receive data transfers. This combination is particularly important in preventing interception or unauthorized access during data transmission.
Access Control and Data Integrity:
Authentication manages access control, ensuring that only verified users can access the system or network. Once inside, encryption ensures that the data they access remains confidential and unaltered. This integration is crucial for maintaining data integrity, as it prevents unauthorized alterations or viewing of sensitive information.
Compliance with Security Standards:
Many industries have strict regulations regarding data security, such as GDPR, HIPAA, and PCI DSS. Integrating encryption and authentication helps organizations comply with these regulations by providing a comprehensive security framework. This not only protects data but also shields organizations from legal and financial repercussions associated with data breaches.
Building Trust and Credibility:
In an era where data breaches are common, customers and stakeholders are increasingly concerned about data security. By integrating encryption and authentication, organizations like ShareArchiver demonstrate a commitment to protecting sensitive information. This builds trust and credibility with customers, partners, and regulatory bodies.
Adaptability to Emerging Threats:
The digital landscape is constantly evolving, with new threats emerging regularly. The combination of encryption and authentication offers a flexible and adaptable security framework. It allows organizations to adjust their security protocols easily to counter new types of cyber threats.
Challenges and Best Practices in Implementing Encryption and Authentication
Let’s evaluate few of the challenges faced in implementation of Encryption and Authentication:
- Complexity of Deployment: Implementing encryption and authentication can be technically complex, especially in large and diverse IT environments. Ensuring compatibility across different systems and platforms can be a challenge.
- Performance Overhead: Encryption, particularly robust methods like AES-256, can slow down system performance due to the additional processing required. This can impact user experience, especially in resource-intensive applications.
- User Compliance and Convenience: Implementing strict authentication methods, like multi-factor authentication (MFA), can sometimes be met with resistance from users due to the perceived inconvenience. Balancing security with ease of use is crucial.
- Key Management: Securely managing the keys used in encryption is a significant challenge. Lost or compromised keys can lead to data breaches or data loss.
- Scalability: As organizations grow, their encryption and authentication needs become more complex. Ensuring that the security measures scale effectively without compromising performance or security is a critical challenge.
Cost Implications: Implementing advanced encryption and authentication methods can be costly. There’s a need to invest in hardware, software, and skilled personnel to manage these systems effectively.
Integrating Encryption and Authentication
The integration of encryption and authentication in data management systems creates a formidable defense mechanism for enhancing data security. While each plays a vital role individually, their combined use provides a more comprehensive and robust security solution. This synergy is crucial in protecting sensitive data from various cyber threats and unauthorized access.
Layered Defense Strategy:
Encryption and authentication work together to create a layered defense strategy. Encryption acts as the first line of defense by encoding the data, making it unreadable to unauthorized users. Authentication adds another layer by controlling who can access the encrypted data. This dual-layer approach significantly reduces the risk of data breaches and unauthorized access.
Securing Data at Rest and in Transit:
Encryption ensures that data is secure both at rest (when stored) and in transit (when being transferred). Authentication enhances this by ensuring that only authorized users can access the data when it’s at rest and can initiate or receive data transfers. This combination is particularly important in preventing interception or unauthorized access during data transmission.
Access Control and Data Integrity:
Authentication manages access control, ensuring that only verified users can access the system or network. Once inside, encryption ensures that the data they access remains confidential and unaltered. This integration is crucial for maintaining data integrity, as it prevents unauthorized alterations or viewing of sensitive information.
Compliance with Security Standards:
Many industries have strict regulations regarding data security, such as GDPR, HIPAA, and PCI DSS. Integrating encryption and authentication helps organizations comply with these regulations by providing a comprehensive security framework. This not only protects data but also shields organizations from legal and financial repercussions associated with data breaches.
Building Trust and Credibility:
In an era where data breaches are common, customers and stakeholders are increasingly concerned about data security. By integrating encryption and authentication, organizations like ShareArchiver demonstrate a commitment to protecting sensitive information. This builds trust and credibility with customers, partners, and regulatory bodies.
Adaptability to Emerging Threats:
The digital landscape is constantly evolving, with new threats emerging regularly. The combination of encryption and authentication offers a flexible and adaptable security framework. It allows organizations to adjust their security protocols easily to counter new types of cyber threats.
Challenges and Best Practices in Implementing Encryption and Authentication
Let’s evaluate few of the challenges faced in implementation of Encryption and Authentication:
- Complexity of Deployment: Implementing encryption and authentication can be technically complex, especially in large and diverse IT environments. Ensuring compatibility across different systems and platforms can be a challenge.
- Performance Overhead: Encryption, particularly robust methods like AES-256, can slow down system performance due to the additional processing required. This can impact user experience, especially in resource-intensive applications.
- User Compliance and Convenience: Implementing strict authentication methods, like multi-factor authentication (MFA), can sometimes be met with resistance from users due to the perceived inconvenience. Balancing security with ease of use is crucial.
- Key Management: Securely managing the keys used in encryption is a significant challenge. Lost or compromised keys can lead to data breaches or data loss.
- Scalability: As organizations grow, their encryption and authentication needs become more complex. Ensuring that the security measures scale effectively without compromising performance or security is a critical challenge.
- Cost Implications: Implementing advanced encryption and authentication methods can be costly. There’s a need to invest in hardware, software, and skilled personnel to manage these systems effectively.
Best Practices for Effective Deployment
Simplify User Experience:
Implement user-friendly authentication methods. For instance, use biometric authentication or single sign-on (SSO) to reduce the complexity for end-users.
Regular Updates and Patch Management:
Keep all systems updated with the latest security patches. This helps in protecting against known vulnerabilities.
Scalable Security Solutions:
Choose encryption and authentication solutions that are scalable. Cloud-based solutions can offer scalability and flexibility.
Efficient Key Management:
Implement robust key management practices. Use automated tools to handle key generation, distribution, storage, and destruction.
Employee Training and Awareness:
Educate employees about the importance of security practices. Regular training can help in maintaining compliance and improving the overall security posture.
Performance Optimization:
Balance encryption strength with system performance. For instance, use lighter encryption methods for less sensitive data to reduce the performance overhead.
Multi-Factor Authentication (MFA):
Implement MFA as it significantly increases security by adding an additional layer of verification.
Regular Security Audits:
Conduct regular security audits to identify vulnerabilities and assess the effectiveness of the encryption and authentication mechanisms in place.
Cost-Benefit Analysis:
Conduct a thorough cost-benefit analysis when choosing security solutions. Investing in the right technology can save costs in the long run by preventing data breaches.
Adapt to Emerging Threats:
Stay informed about the latest cyber threats and adapt security measures accordingly. Continuous improvement and adaptation are key to maintaining robust security.
Conclusion
Implementing encryption and authentication effectively is not just a technical requirement but a fundamental aspect of building trust and maintaining integrity in our digital interactions. While challenges such as deployment complexity, user compliance, and scalability persist, the adoption of best practices offers a pathway to overcoming these hurdles.
The integration of strong encryption and authentication is more than just a defensive measure; it’s a commitment to safeguarding the digital library of our personal and professional lives. In this era of incessant digital advancements, such a commitment is not just beneficial but essential for the sustained growth and trust in our digital world.